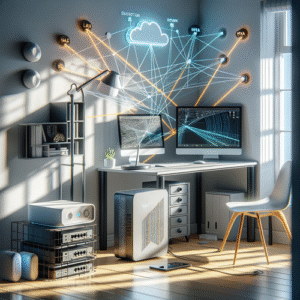
Split Tunneling VPN Keeping LAN Access and Internet
Why Split Tunneling VPN Matters for Your Home Network
Imagine this: you’re connected to your VPN for online privacy or to access work resources, but suddenly your smart lights or NAS stop responding. What gives? Simple — your VPN is routing all your traffic, including local LAN requests, through the tunnel. That means your devices on the home network can no longer see each other directly.
This is a common frustration for home enthusiasts juggling privacy, remote access, and smart home convenience. That’s where split tunneling shines — it lets you send some traffic through your VPN (like internet-bound data) while keeping local LAN access direct and hassle-free.
In this article, we’ll explore how split tunneling works, why you’d want to use it with UniFi and VLANs, and practical tips to get it running smoothly.
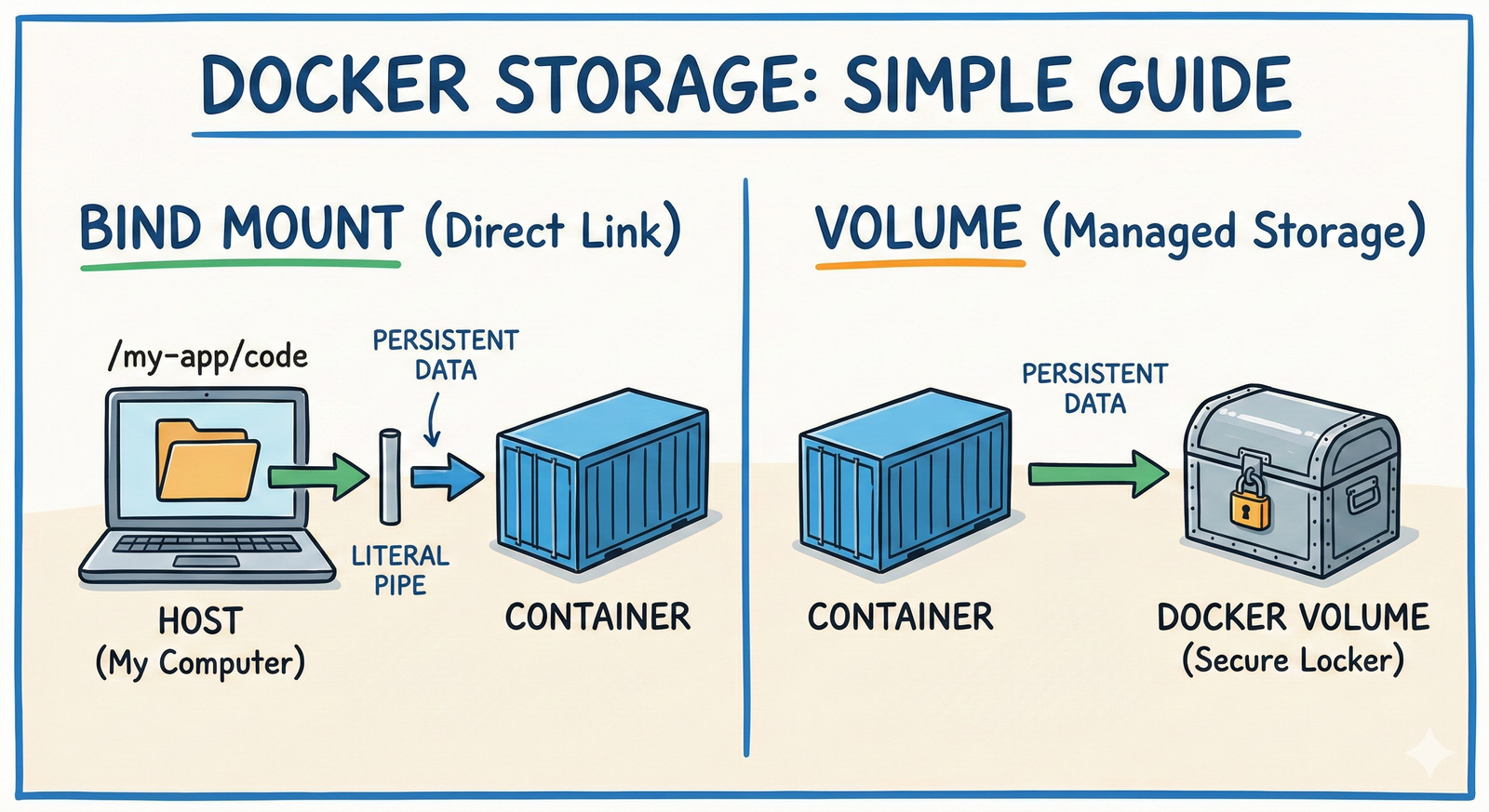
What is Split Tunneling Anyway?
Split tunneling is a VPN feature that splits the network traffic into two streams:
- VPN Tunnel: Traffic destined for the internet or specific networks goes through the VPN.
- Direct LAN Traffic: Local network traffic stays on your local network, bypassing the VPN.
This is different from a full tunnel VPN, where all your traffic—local and internet—is sent through the VPN gateway.
Why Use Split Tunneling?
- Access your LAN devices like printers, NAS, smart TVs, or home automation hubs without VPN interference.
- Keep WAN traffic private by routing internet traffic through your VPN provider or corporate VPN.
- Improve performance because local requests don’t waste VPN bandwidth or add latency.
- Avoid VPN device lockout scenarios where local management tools stop working.
Think of a VPN tunnel like a toll bridge. Full tunneling forces all your cars (traffic) onto the bridge, even if you just want to visit next door (LAN). Split tunneling lets you choose the bridge only for the long haul (internet), letting local trips stay on surface streets.
How Split Tunneling Works with UniFi and VLANs
If you’re in the UniFi ecosystem, you likely have VLANs managing network segments — say one VLAN for your IoT devices, another for your work laptops, etc. Split tunneling can complement this by controlling where VPN traffic flows from each VLAN or device.
Typical Setup:
-
VPN Client Configuration: Your device’s VPN client must support split tunneling. Some popular options: OpenVPN, WireGuard, or built-in VPN clients with route exclusions.
-
Routing Table Rules: Define routes that specify which traffic should bypass the VPN. For example, the LAN range like
192.168.1.0/24is routed locally. -
UniFi Network Settings: Configure firewall rules and VLAN routing so that traffic destined for your LAN is accessible without forcing it into the VPN.
-
VPN Server Settings: Ensure your VPN server isn’t forcing routes that conflict with split tunnel rules, especially “redirect-gateway” directives that push all traffic VPN-side.
How UniFi Helps:
- UniFi’s firewall and routing rules let you finely control inter-VLAN routing, which pairs nicely with split tunneling on client devices.
- You can set policy routing per VLAN or per firewall rule to decide which traffic uses the VPN.
- The UniFi Network Controller makes managing these rules more visual and less command-line heavy.
Practical Example: Home Office with Split Tunneling
Here’s a scenario from my setup:
- I have a Work VLAN (VLAN 20) for my laptop.
- IoT devices and NAS sit in VLAN 10.
- When connected to my OpenVPN server on my UniFi Dream Machine Pro:
- Internet traffic routes through the VPN for privacy.
- LAN traffic, like accessing my NAS at
192.168.10.x, goes directly without hitting the VPN.
How I Set It Up:
- On the client: I configured OpenVPN with the
route-nopulloption to stop it from redirecting all traffic. - Add LAN route on VPN client: I added a manual route for
192.168.10.0/24pointing to the LAN gateway. - UniFi firewall and routing: I made sure VLAN 20 can reach VLAN 10 locally.
- VPN server config: Removed any
push "redirect-gateway"lines, letting the client decide what is routed through VPN.
This setup kept my home devices easily reachable while my internet traffic was encrypted and anonymized.
Common Gotchas When Using Split Tunneling
- Forgetting to add local network routes on the VPN client: Without these, your device sends LAN traffic through VPN, causing latency or failure.
- VPN server pushing full tunnel routes: If the server forces clients to route all traffic through VPN, split tunneling won’t work without tweaking.
- Misconfigured firewall rules: UniFi firewalls are powerful but tricky — an overly strict rule can block your LAN access.
- DNS leaks: Sometimes your DNS queries leak outside VPN or don’t resolve local hostnames. Using local DNS or split tunneling DNS configurations helps.
- Overlapping IP ranges: If your home LAN and VPN server networks overlap, routing can get confusing or break local access.
When Split Tunneling Might Not Be Ideal
- Security-first environments: If your company or your own security policy requires all traffic to be monitored or encrypted, split tunneling defeats that purpose.
- Public Wi-Fi without trusted LAN: If you’re on an untrusted network, routing local traffic outside the VPN can expose you.
- Complex routing needs: If your VPN needs include accessing internal resources only, or you have complex multi-hop routing, managing split tunnel routes might get tricky.
In such cases, a full tunnel with additional local exceptions (like device-specific firewall rules) might be preferable.
Key Takeaway
Split tunneling is a powerful middle ground for VPN users who want privacy and access simultaneously. With UniFi’s flexible VLAN and firewall capabilities, you can craft a neat network where your internet traffic takes the safe VPN highway while your smart home devices stay just a hop away on your local subnet.
If you’re running into the frustrating case where VPN kills your LAN access, check your VPN client routing rules, UniFi VLAN firewalls, and VPN server config for split tunneling options. Smart split tunneling will have your traffic flow just right, letting you work and play without network headaches.
In my experience, spending a little time setting this up pays off big on convenience and peace of mind. Give it a go, and your Wi-Fi-connected kettle and NAS will thank you!







Post Comment