Why These Common Vulnerabilities Keep Ethical Hackers Busy
The Persistent Landscape of Common Vulnerabilities
In the ever-evolving world of cybersecurity, certain issues seem to persistently demand the attention of ethical hackers. These common vulnerabilities serve as gateways for malicious actors, making them a perpetual challenge for security professionals. Understanding why these vulnerabilities remain so prevalent, despite advancements in technology and awareness, sheds light on the complex nature of securing digital environments. Ethical hackers continually focus on these weaknesses to help organizations strengthen defenses and protect sensitive data.
Why Common Vulnerabilities Remain Unresolved
Even with modern security tools and frameworks, some vulnerabilities continue to be exploited. The reasons behind their persistence are multifaceted:
Complexity of Systems
Modern IT infrastructures have grown increasingly complex. With layers of applications, networks, and third-party integrations, vulnerabilities can arise in unexpected places. This complexity makes exhaustive vulnerability identification and remediation difficult.
– Expanding attack surfaces due to cloud adoption and remote work
– Legacy systems interacting with newer technologies
– Lack of centralized oversight across disparate systems
Human Factor and Misconfigurations
Despite sophisticated technology, human error remains a significant source of weaknesses.
– Incorrect server or software configurations
– Inadequate updates and patch management
– Weak password policies and poor access controls
Ethical hackers target these areas because they consistently lead to exploitable points in networks.
Common Vulnerabilities that Keep Ethical Hackers Busy
Certain types of vulnerabilities repeatedly challenge cybersecurity experts. Ethical hackers prioritize these common vulnerabilities in their testing and assessments.
Injection Flaws
Injection vulnerabilities, such as SQL injection and command injection, occur when untrusted data is sent to an interpreter. This enables attackers to execute unauthorized commands or access data illicitly.
– SQL injection allows attackers to manipulate backend databases
– Command injection enables arbitrary command execution on servers
Preventing these requires rigorous input validation and parameterized queries.
Broken Access Controls
Improperly enforced access controls let unauthorized users access restricted data or functions. Ethical hackers frequently find these flaws in web applications and APIs.
– Missing or ineffective authorization checks
– Excessive permissions granted to users
– Insecure direct object references allowing data exposure
Implementing the principle of least privilege and thorough access testing can mitigate these risks.
The Role of Ethical Hackers in Addressing Common Vulnerabilities
Ethical hackers employ proactive strategies designed to expose and help remediate common vulnerabilities before malicious hackers can exploit them.
Vulnerability Scanning and Penetration Testing
Regular scanning and penetration testing help identify vulnerabilities early. Ethical hackers:
– Use automated tools to detect known security weaknesses
– Perform manual testing to uncover complex logic flaws
– Simulate real-world attack scenarios to assess security posture
Collaboration with Development Teams
Identifying vulnerabilities is only part of the solution. Ethical hackers often work alongside developers to:
– Prioritize vulnerabilities based on risk
– Provide detailed remediation guidance
– Assist in implementing secure coding practices
This partnership enhances the overall security lifecycle.
The Impact of Emerging Technologies on Common Vulnerabilities
New technologies introduce both opportunities and risks for security.
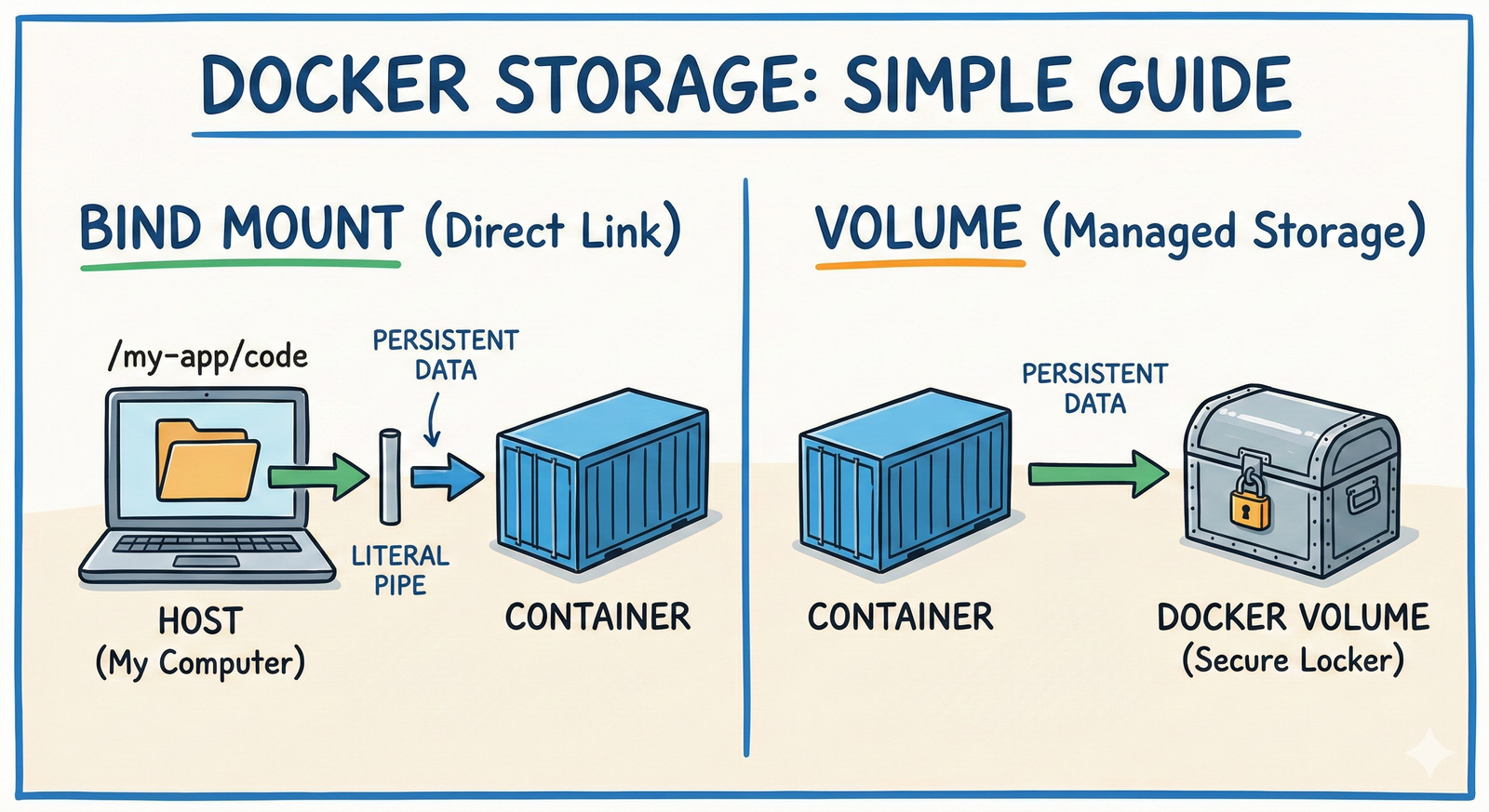
Cloud and Containerization
Moving infrastructure to the cloud and using containers alters vulnerability landscapes.
– Misconfigured cloud storage buckets leading to data leaks
– Insecure container images exposing sensitive information
Ethical hackers monitor these evolving threats to advise on best practices.
Internet of Things (IoT)
The proliferation of IoT devices increases attack vectors.
– Weak default credentials
– Unencrypted communications
– Lack of firmware updates
These common vulnerabilities require fresh focus from security professionals.
Best Practices to Mitigate Common Vulnerabilities
Addressing common vulnerabilities demands a comprehensive approach. Organizations should adopt these practices:
– Regularly patch and update systems and applications
– Enforce strong authentication and access controls
– Conduct continuous security training for employees
– Implement secure coding standards and code reviews
– Utilize automated scanning coupled with manual penetration testing
– Monitor systems actively to detect anomalies promptly
By integrating these strategies, organizations can significantly reduce exposure to common vulnerabilities.
Resources for Staying Ahead of Common Vulnerabilities
Keeping informed about emerging threats and best practices is crucial:
– National Vulnerability Database (https://nvd.nist.gov)
– OWASP Top Ten Project for web security risks
– SANS Institute’s cybersecurity resources
– Cybersecurity blogs and forums for up-to-date insights
Ethical hackers leverage these tools to maintain cutting-edge skills and knowledge.
Strengthening Security Through Persistent Vigilance
Common vulnerabilities continue to challenge organizations because they often arise from complex technologies and human factors. Ethical hackers remain focused on these areas because closing these gaps is essential for robust cybersecurity. By understanding the nature of these vulnerabilities and adopting proactive measures, businesses can protect themselves against evolving threats.
Take the next step to fortify your security by engaging with ethical hacking professionals or implementing continuous vulnerability assessments tailored to your environment. Staying ahead of common vulnerabilities is not just an option but a necessity in today’s digital landscape.






Post Comment