Why These Common Vulnerabilities Still Trip Up Ethical Hackers
What Makes Common Vulnerabilities a Persistent Challenge?
Despite the rapid evolution of cybersecurity tools and techniques, many common vulnerabilities continue to pose significant challenges for ethical hackers. These persistent weaknesses often arise from fundamental flaws in design, implementation, or maintenance that remain unpatched or unnoticed. Understanding why these vulnerabilities endure helps ethical hackers anticipate and counter threats more effectively.
One reason is that many vulnerabilities originate from outdated assumptions about software security. Developers might rely on legacy code or standardized libraries without thoroughly analyzing their security implications. In addition, resource limitations can lead to shortcuts in testing and scrutiny, allowing weaknesses to slip through. Even with automated scanning and advanced penetration testing frameworks, the subtleties of common vulnerabilities—like business logic flaws or misconfigured services—can evade detection.
Another factor is the dynamic nature of technology deployments. As organizations rapidly adopt cloud infrastructures, Internet of Things (IoT) devices, and complex APIs, new attack surfaces emerge. Common vulnerabilities that were once straightforward to identify now intertwine with intricate environments, complicating ethical hackers’ detection efforts.
The Most Common Vulnerabilities and Why They Trip Up Ethical Hackers
The landscape of common vulnerabilities is vast, but several categories frequently cause issues during ethical hacking engagements. Knowing these helps security professionals prioritize testing and enhance protection strategies.
Injection Flaws: SQL, Command, and Beyond
Injection vulnerabilities rank among the oldest yet most recurrent pitfalls. Despite being well-documented, SQL injection, command injection, and other variants still catch ethical hackers off guard because:
– Applications may inadequately sanitize inputs, especially in legacy or third-party components.
– Complex query structures or multi-layered frameworks obscure vulnerable spots.
– Automated tools sometimes miss blended injection opportunities, such as NoSQL or LDAP injection.
Practical example: An enterprise web app utilizing dynamic SQL queries without proper parameterization can allow a hacker to manipulate database commands, exposing sensitive data.
Broken Authentication and Session Management
Authentication issues, including weak password policies, improper session invalidation, and exposure of credentials, remain a stumbling block. Ethical hackers find these vulnerabilities challenging because:
– Modern authentication flows incorporate multifactor systems that introduce varied failure points.
– Sessions that persist too long or are transmitted insecurely create exploitable conditions not always obvious in initial scans.
– Attackers may use social engineering or credential stuffing in ways that automated tools don’t simulate effectively.
Misconfigured Security Settings
Misconfigurations rank high among common vulnerabilities. These include excessive permissions, open cloud storage buckets, or default credentials left unchanged. Ethical hackers can overlook these if they don’t assess beyond standard test cases because:
– Organizational complexity causes unclear boundary definitions for security policies.
– Rapid deployment cycles leave little time for detailed configuration reviews.
– Scanners may not detect nuanced misconfigurations linked to infrastructure as code or container settings.
Why Detection Tools Sometimes Miss Common Vulnerabilities
Even the most sophisticated scanning software can fail to identify certain common vulnerabilities, frustrating ethical hackers.
Limitations of Automated Scanners
Automated tools use signature-based detection, logical flow analysis, and heuristics, yet they can miss:
– Context-dependent flaws that require understanding business logic.
– Chained vulnerabilities where multiple small issues combine to produce a significant exploit.
– Injection vectors masked by encoding or obfuscation.
Ethical hackers should complement automated scans with manual analysis to uncover overlooked problems.
The Importance of Manual Testing
Manual penetration testing remains critical in revealing vulnerabilities that tools miss. Ethical hackers apply their expertise by:
– Crafting custom payloads targeting non-standard inputs.
– Analyzing source code or reverse engineering binary files for hidden issues.
– Performing social engineering or environment-specific checks that automated systems cannot replicate.
This hands-on approach demands skilled professionals with deep knowledge of common vulnerabilities and attack methodologies.
How Shifting Technology Trends Impact Common Vulnerabilities
Technological advancements both mitigate and introduce complexities related to common vulnerabilities.
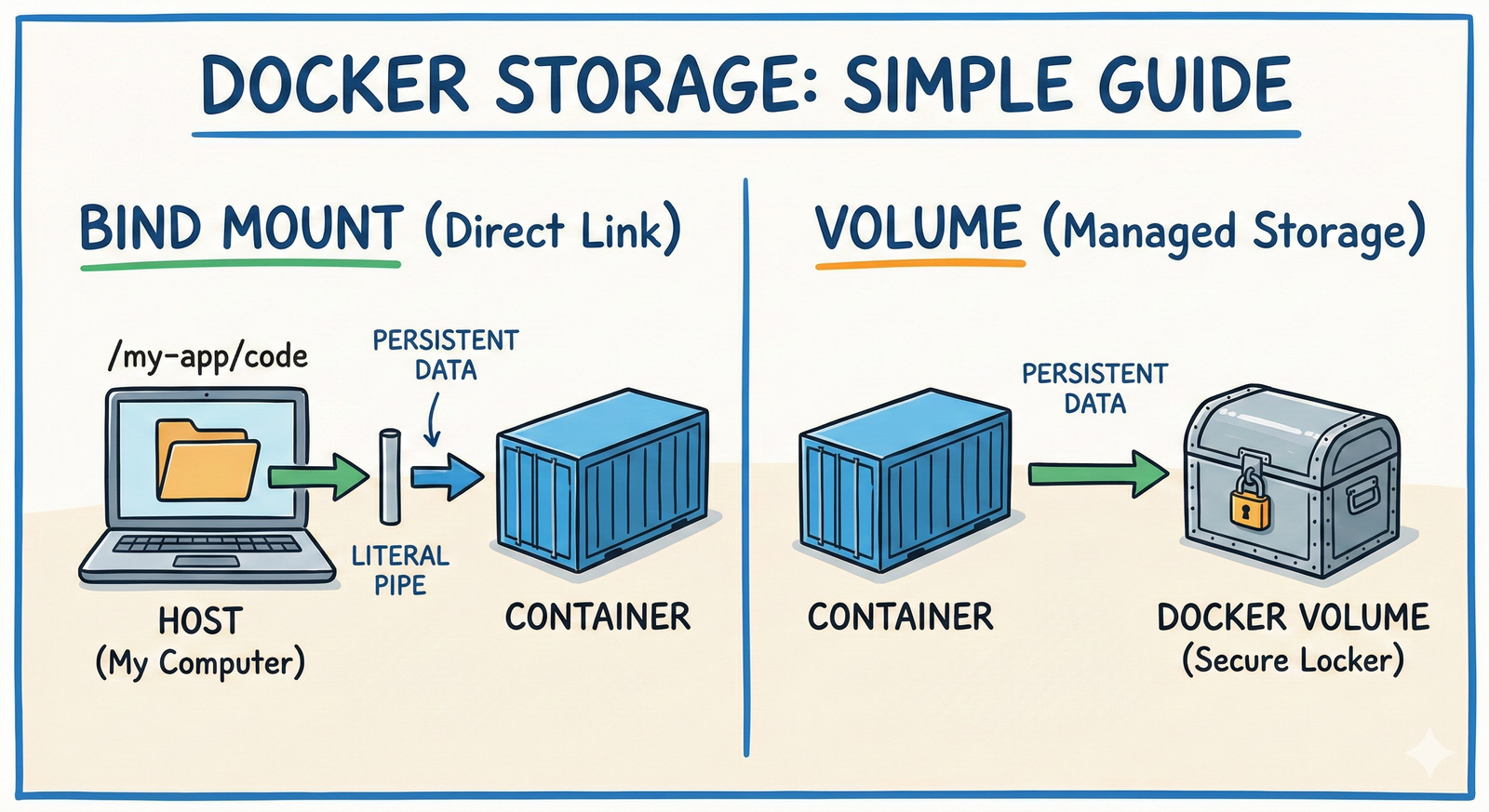
Cloud Environments and Containerization
As organizations migrate to cloud platforms and embrace containers like Docker and Kubernetes, new vulnerability vectors appear:
– Misconfigured Identity and Access Management (IAM) roles can expose resources.
– Insecure container images may contain outdated libraries with known vulnerabilities.
– Network segmentation errors allow lateral movement inside cloud infrastructure.
Ethical hackers must adapt testing strategies accordingly to address these novel risks.
The Rise of APIs and Microservices
The proliferation of APIs and microservices architectures offers increased functionality but also creates multiple attack surfaces. Common vulnerabilities here include:
– Insufficient input validation in API endpoints.
– Broken object-level authorization allowing data exposure.
– Inconsistent authentication mechanisms across services.
Comprehensive testing of API security is essential for identifying these hidden pitfalls.
Best Practices to Overcome Challenges with Common Vulnerabilities
Addressing persistent common vulnerabilities requires a combination of technical expertise, process improvements, and collaboration.
Implement Rigorous Code Review and Security Testing
– Integrate static and dynamic analysis tools into the development lifecycle.
– Enforce peer code reviews focused on security considerations.
– Use fuzz testing to discover input-handling issues.
Maintain Up-to-Date Knowledge and Training
– Keep abreast of the latest vulnerability disclosures and exploitation techniques.
– Participate in ethical hacking communities and continuous education.
– Conduct regular internal security training for developers and testers.
Adopt a Proactive Security Culture
– Establish cross-functional teams to monitor and respond to vulnerabilities promptly.
– Automate patch management for software and infrastructure components.
– Perform periodic red team exercises simulating advanced attacks.
These practices reduce the likelihood of common vulnerabilities undermining the security posture.
Leveraging Resources to Stay Ahead of Common Vulnerabilities
Ethical hackers benefit immensely from tapping into community resources and authoritative databases.
– The Open Web Application Security Project (OWASP) offers comprehensive guidance on top common vulnerabilities and mitigation strategies.
– The National Vulnerability Database tracks publicly disclosed software weaknesses, enabling targeted testing.
– Platforms like HackerOne and Bugcrowd provide real-world insights into emerging vulnerabilities through bug bounty programs.
Continual engagement with these resources enhances ethical hackers’ ability to anticipate and address common vulnerabilities effectively.
Wrapping Up the Persistent Puzzle of Common Vulnerabilities
Common vulnerabilities continue to challenge ethical hackers due to their deeply rooted nature, evolving technical landscapes, and the limitations of detection tools. Overcoming these hurdles requires a blend of automated and manual testing, ongoing education, and an organizational commitment to security. By concentrating on thorough assessment, embracing new technologies wisely, and maintaining strong collaboration, ethical hackers can significantly reduce the risk posed by these enduring weaknesses.
If you’re looking to deepen your knowledge or equip your team with cutting-edge ethical hacking skills, explore specialized training programs and stay active in security forums. Addressing common vulnerabilities is an ongoing effort—starting now can make all the difference in safeguarding your digital assets.






Post Comment